Ransomware attacks have become one of the most disruptive threats to modern businesses. A single incident can halt operations, compromise data, and damage trust. Many organizations lack the resources or expertise to respond quickly on their own. An IT Company in St. Louis providing managed IT services plays a critical role in handling ransomware incidents with speed and structure. They combine preparation, response, and recovery into a clear process. This article explains how managed IT services handle ransomware response while minimizing disruption and restoring stability.
Understanding the Ransomware Threat Landscape
 Ransomware continues to evolve in complexity and frequency. Attackers target networks, endpoints, and cloud systems. Phishing emails, weak passwords, and unpatched software often serve as entry points. Once inside, malware encrypts data and demands payment. The impact spreads quickly across systems. Managed IT services stay informed about emerging threats. This awareness helps them prepare defenses before attacks occur and respond effectively when incidents happen.
Ransomware continues to evolve in complexity and frequency. Attackers target networks, endpoints, and cloud systems. Phishing emails, weak passwords, and unpatched software often serve as entry points. Once inside, malware encrypts data and demands payment. The impact spreads quickly across systems. Managed IT services stay informed about emerging threats. This awareness helps them prepare defenses before attacks occur and respond effectively when incidents happen.
Early Detection and Threat Identification
Fast detection limits damage. Managed IT services use continuous monitoring tools to identify unusual activity. Sudden file encryption, abnormal network traffic, or unauthorized access trigger alerts. Early detection allows teams to act before ransomware spreads further. Automated systems support human oversight. This combination improves accuracy and speed. Identifying the threat early is critical to protecting data and limiting operational downtime.
Immediate Containment and System Isolation
Once ransomware is detected, containment becomes the priority. Managed IT teams isolate affected systems from the network. This step prevents malware from reaching other devices or servers. Access points may be temporarily restricted. Infected endpoints are taken offline. Clear procedures guide these actions. Swift isolation helps ensure the attack remains limited and manageable rather than widespread.
Incident Response Coordination and Communication
Effective response requires coordination. Managed IT services follow predefined incident response plans. Roles and responsibilities are clear. Internal teams receive timely updates. External partners may also be informed when needed. Communication stays calm and factual. This structure reduces confusion during stressful situations. A unique benefit of managed services is having experienced responders lead the process without delay.
Data Recovery and Backup Restoration
Recovery focuses on restoring systems safely. Managed IT services rely on secure and tested backups. Clean data is restored after infected systems are wiped. Recovery follows a controlled sequence to avoid reinfection. Backup integrity is verified before use. This process reduces the need to consider ransom payments. Reliable recovery methods help businesses resume operations with confidence and minimal data loss.
Security Hardening After the Attack

After recovery, systems are strengthened. Managed IT providers analyze how the attack occurred. Vulnerabilities are identified and addressed. Patches are applied and access controls reviewed. Security policies may be updated. Additional monitoring tools can be introduced. These steps help ensure the same weakness is not exploited again. Strengthening defenses is a vital part of long-term protection.
Compliance and Legal Considerations
Ransomware incidents may involve regulatory obligations. Managed IT services help navigate compliance requirements. Data breach notifications are assessed carefully. Documentation is prepared to support audits or investigations. Legal and insurance partners may be involved. Proper handling reduces the risk of penalties. Accurate records also support transparency with customers and stakeholders during recovery.
Preparedness Planning and Ongoing Prevention
Prevention remains the strongest defense. Managed IT services provide ongoing training and system reviews. Employees learn to recognize phishing attempts. Backup strategies are tested regularly. Incident response plans are refined over time. Continuous improvement helps ensure readiness. Preparedness shows utmost commitment to resilience and operational continuity in a threat-filled environment.
Managed IT services bring structure and expertise to ransomware response. From early detection to full recovery, each step follows a clear process. Businesses benefit from faster containment, safer recovery, and stronger defenses. The approach reduces panic and limits damage. With professional support, organizations can face ransomware threats with greater confidence. Managed IT services help ensure systems remain secure, resilient, and prepared for future challenges in an increasingly hostile digital world.



 It will be difficult to identify the pros and cons of the drums just by looking at it. Therefore, when you read the reviews before hand, you get to know about the good and bad side of the drum. Through, the pros and cons you will decide on the drum that is appropriate for your needs. You can leave out the drum that has a lot of cons and goes for the one with a lot of positives. Using the review, you can determine whether you can compromise on the disadvantages and still buy the drum or not.
It will be difficult to identify the pros and cons of the drums just by looking at it. Therefore, when you read the reviews before hand, you get to know about the good and bad side of the drum. Through, the pros and cons you will decide on the drum that is appropriate for your needs. You can leave out the drum that has a lot of cons and goes for the one with a lot of positives. Using the review, you can determine whether you can compromise on the disadvantages and still buy the drum or not. Getting a drum with the features you want can be a daunting task if you do not have where to start from. However, through reading a review, you can see the features of the product before you make a purchase. It will be easier to determine the drum set that has all the exact features that you want. There is no need to choose a drum without first considering the features it has to offer. The only thing you have to do is just read the review, and you will be on your way to getting the right drum.
Getting a drum with the features you want can be a daunting task if you do not have where to start from. However, through reading a review, you can see the features of the product before you make a purchase. It will be easier to determine the drum set that has all the exact features that you want. There is no need to choose a drum without first considering the features it has to offer. The only thing you have to do is just read the review, and you will be on your way to getting the right drum.
 every time he holds the mouse. The other challenge that most of the people out there face is that most of the mouse have the same shape and size whereas the users have different hand sizes.
every time he holds the mouse. The other challenge that most of the people out there face is that most of the mouse have the same shape and size whereas the users have different hand sizes. There are lots of advantages of using the ergonomic mouse over the standard keyboard and mouse. One of the benefits is that the right peripheral can minimize the tension that the hand and the wrist are usually subjected to. It helps reduce the strain on the arm and therefore the resultant pain which is the back and the neck pains. People are more productive and efficient of they maintain their natural hand position.
There are lots of advantages of using the ergonomic mouse over the standard keyboard and mouse. One of the benefits is that the right peripheral can minimize the tension that the hand and the wrist are usually subjected to. It helps reduce the strain on the arm and therefore the resultant pain which is the back and the neck pains. People are more productive and efficient of they maintain their natural hand position.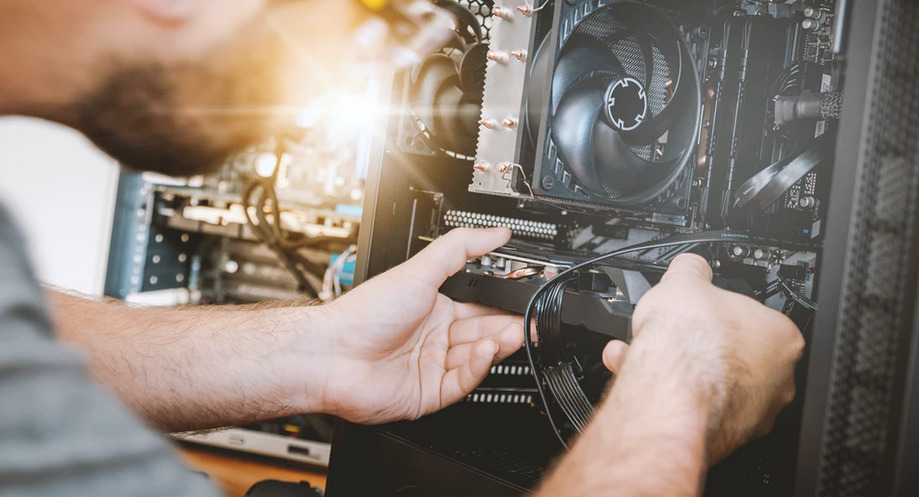
 The first factor you should consider when choosing a computer repair service is the warranty. As many computer owners have come to know, some problems regarding computers can reoccur severally. This mostly happens when the repair service one chooses does not offer quality solutions.
The first factor you should consider when choosing a computer repair service is the warranty. As many computer owners have come to know, some problems regarding computers can reoccur severally. This mostly happens when the repair service one chooses does not offer quality solutions. It is also crucial to consider the reputation of a computer repair service provider. Different computer repair services will have reputations that vary. It is crucial to select a repair service with a great reputation to increase your chances of getting an ideal service.
It is also crucial to consider the reputation of a computer repair service provider. Different computer repair services will have reputations that vary. It is crucial to select a repair service with a great reputation to increase your chances of getting an ideal service.